���ӌ�(sh��)�F(xi��n).net������M(j��n)��ע��_.Net�̳�
���]�������.NET�h(hu��n)����W(w��ng)վ����IP�^(gu��)�V�����A�ܼ��F(tu��n)��ij�l(f��)늏S����I(y��)�W(w��ng)վ������Asp.Net2.0��(sh��)�F(xi��n)�������S��Դ����Ҫ��(sh��)�F(xi��n)�S��(n��i)�Ñ���ֱ���L��(w��n)����(g��)վ�c(di��n)�������(y��)�棬�S���Ñ�ֻ���L��(w��n)ָ�����(y��)��Ĺ��ܣ����Č�������������������O(sh��)Ӌ(j��)�����a��(sh��)�F(xi��n)������(y��ng)�õ�������U������(g��)��Q�������γ��^(gu��)�̡� 1.
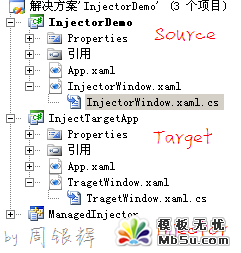
�M(j��n)��ע����^��Ҋ(ji��n),������IDE�{(di��o)ԇ
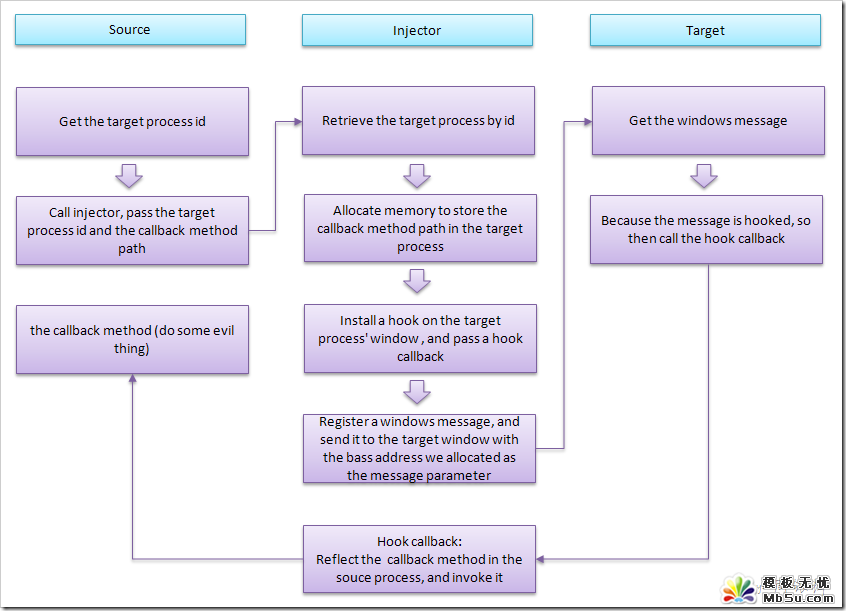
��������ԭ�����@�ӵ�:
����Դ�M(j��n)��(Ҳ������Ĵ��a���ڵ��M(j��n)��)�@��Ŀ��(bi��o)�M(j��n)��(Ҳ�������ע��Ŀ��(bi��o)���ڵ��M(j��n)��)��ID���M(j��n)�̌�(du��)��
����Դ�M(j��n)���ṩһ���{(di��o)����(sh��)methodA(Ҳ��������Ҫע�뵽Ŀ��(bi��o)�M(j��n)�̺�����(zh��)�еĴ��a)
������Ŀ��(bi��o)�M(j��n)�̺ͻ��{(di��o)����(sh��)methodA������·��(�����ڵ�Assembly,Classic�Լ�MethodName)�ύ�oInjector(Ҳ�����҂�����(xi��)��ؓ(f��)؟(z��)ע����),Injector��(l��i)���ע���Ŀ��(bi��o)�M(j��n)�̈�(zh��)�л��{(di��o)����(sh��)
����Injector����(j��)�ṩ��Ŀ��(bi��o)�M(j��n)��IDȡ��Ŀ��(bi��o)�M(j��n)�̌�(du��)��,���@��Ŀ��(bi��o)�M(j��n)�̵�һ��(g��)����(�҂��Q��Ŀ��(bi��o)����)
������Ŀ��(bi��o)�����з���һ�K��(n��i)��,�����{(di��o)����(sh��)methodA������·�������ַ�������ԓ��(n��i)����
����Injector��Ŀ��(bi��o)�M(j��n)���а��bһ��(g��)�^��(Hook)�O(ji��n)ҕijһ��(g��)Windows��Ϣ(messageA),��(xi��)�^�ӵĻ��{(di��o)����(sh��)methodB(ԓ�����еă�(n��i)���Ժ���)
������Ŀ��(bi��o)�M(j��n)�̰l(f��)��ϢmessageA,�������ŷ���ă�(n��i)��Ļ���ַ������Ϣ����(sh��)���f.
���������҂�ᘌ�(du��)messageA���b���^��,����Ŀ��(bi��o)�M(j��n)�̕�(hu��)�{(di��o)���҂��^�Ӻ���(sh��)methodB,����(hu��)�ѷ���ă�(n��i)��Ļ���ַ�����ں���(sh��)����(sh��)��
���������@��(g��)�D���ܕ�(hu��)���������������Ԓ:��
���������DƬ���������Ո(q��ng)�c(di��n)���@��鿴ԭ�D����D����
#include "stdafx.h"
#include "Injector.h"
#include <vcclr.h>
using namespace ManagedInjector;
//defines a new window message that is guaranteed to be unique throughout the system.
//The message value can be used when sending or posting messages.
static unsigned int WM_GOBABYGO = ::RegisterWindowMessage(L"Injector_GOBABYGO!");
static HHOOK _messageHookHandle;
//-----------------------------------------------------------------------------
//Spying Process functions follow
//-----------------------------------------------------------------------------
void Injector::Launch(System::IntPtr windowHandle, System::Reflection::Assembly^ assembly, System::String^ className, System::String^ methodName) {
������ System::String^ assemblyClassAndMethod = assembly->Location + "$" + className + "$" + methodName;
������ //convert String to local wchar_t* or char*
������ pin_ptr<const wchar_t> acmLocal = PtrToStringChars(assemblyClassAndMethod);
������ //Maps the specified executable module into the address space of the calling process.
������ HINSTANCE hinstDLL = ::LoadLibrary((LPCTSTR) _T("ManagedInjector.dll"));
������ if (hinstDLL)
������ {
�������������� DWORD processID = 0;
�������������� //get the process id and thread id
�������������� DWORD threadID = ::GetWindowThreadProcessId((HWND)windowHandle.ToPointer(), &processID);
�������������� if (processID)
�������������� {
���������������������� //get the target process object (handle)
���������������������� HANDLE hProcess = ::OpenProcess(PROCESS_ALL_ACCESS, FALSE, processID);
���������������������� if (hProcess)
���������������������� {
������������������������������ int buffLen = (assemblyClassAndMethod->Length + 1) * sizeof(wchar_t);
������������������������������ //Allocates physical storage in memory or in the paging file on disk for the specified reserved memory pages.
������������������������������ //The function initializes the memory to zero.
������������������������������ //The return value is the base address of the allocated region of pages.
������������������������������ void* acmRemote = ::VirtualAllocEx(hProcess, NULL, buffLen, MEM_COMMIT, PAGE_READWRITE);
������������������������������ if (acmRemote)
������������������������������ {
�������������������������������������� //copies the data(the assemblyClassAndMethod string)
�������������������������������������� //from the specified buffer in the current process
�������������������������������������� //to the address range of the target process
�������������������������������������� ::WriteProcessMemory(hProcess, acmRemote, acmLocal, buffLen, NULL);
������������������������������
�������������������������������������� //Retrieves the address of MessageHookProc method from the hintsDLL
�������������������������������������� HOOKPROC procAddress = (HOOKPROC)GetProcAddress(hinstDLL, "MessageHookProc");
�������������������������������������� //install a hook procedure to the target thread(before the system sends the messages to the destination window procedure)
�������������������������������������� _messageHookHandle = ::SetWindowsHookEx(WH_CALLWNDPROC, procAddress, hinstDLL, threadID);
�������������������������������������� if (_messageHookHandle)
�������������������������������������� {
���������������������������������������������� //send our custom message to the target window of the target process
���������������������������������������������� ::SendMessage((HWND)windowHandle.ToPointer(), WM_GOBABYGO, (WPARAM)acmRemote, 0);
���������������������������������������������� //removes the hook procedure installed in a hook chain by the SetWindowsHookEx function.
���������������������������������������������� ::UnhookWindowsHookEx(_messageHookHandle);
�������������������������������������� }
�������������������������������������� //removes a hook procedure installed in a hook chain by the SetWindowsHookEx function.
�������������������������������������� ::VirtualFreeEx(hProcess, acmRemote, buffLen, MEM_RELEASE);
������������������������������ }
������������������������������ ::CloseHandle(hProcess);
���������������������� }
�������������� }
�������������� //Decrements the reference count of the loaded DLL
�������������� ::FreeLibrary(hinstDLL);
������ }
}
__declspec( dllexport )
// The procedure for hooking, this will be called back after hooked
int __stdcall MessageHookProc(int nCode, WPARAM wparam, LPARAM lparam) {
������ //HC_ACTION: indicate that there are argments in wparam and lparam
������ if (nCode == HC_ACTION)
������ {
�������������� CWPSTRUCT* msg = (CWPSTRUCT*)lparam;
�������������� //when the target window received our custom message
�������������� if (msg != NULL && msg->message == WM_GOBABYGO)
�������������� {
���������������������� //get the argument passed by the message
���������������������� //actually, the argument is the base address (a pointer)
���������������������� //of the assemblyClassAndMethod string in the target process memory
���������������������� wchar_t* acmRemote = (wchar_t*)msg->wParam;
���������������������� //gcnew: creates an instance of a managed type (reference or value type) on the garbage collected heap
���������������������� System::String^ acmLocal = gcnew System::String(acmRemote);
���������������������� //split the string into substring array with $. Under this context:
���������������������� //acmSplit[0]:the assembly's location
���������������������� //acmSplit[1]:className;
���������������������� //acmSplit[2]:methodName
���������������������� //we use these infomation to reflect the method in the source assembly, and invoke it in the target process
���������������������� cli::array<System::String^>^ acmSplit = acmLocal->Split('$');
���������������������� //refect the method, and invoke it
���������������������� System::Reflection::Assembly^ assembly = System::Reflection::Assembly::LoadFile(acmSplit[0]);
���������������������� if (assembly != nullptr)
���������������������� {
������������������������������ System::Type^ type = assembly->GetType(acmSplit[1]);
������������������������������ if (type != nullptr)
������������������������������ {
�������������������������������������� System::Reflection::MethodInfo^ methodInfo =
���������������������������������������������� type->GetMethod(acmSplit[2], System::Reflection::BindingFlags::Static | System::Reflection::BindingFlags::Public);
�������������������������������������� if (methodInfo != nullptr)
�������������������������������������� {
���������������������������������������������� methodInfo->Invoke(nullptr, nullptr);
�������������������������������������� }
������������������������������ }
���������������������� }
�������������� }
������ }
������ return CallNextHookEx(_messageHookHandle, nCode, wparam, lparam);
}����(l��i),����(g��)DEMO�Lԇһ��:��
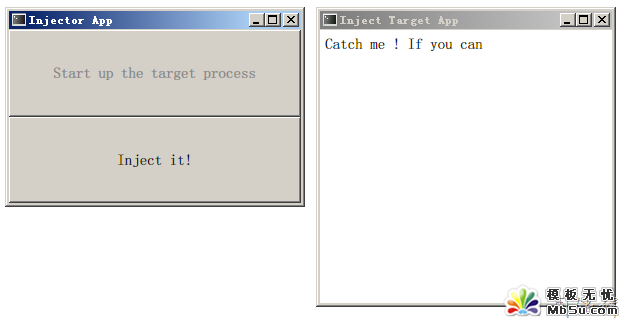
 ����
����
������Q�����е�InjectorDemo�����҂�������Դ�M(j��n)��,����(hu��)����Injector�������@�δ��aע�뵽Target�M(j��n)���в���(zh��)��:
public static void DoSomethingEvie()
{
������ vartargetWindow = Application.Current.MainWindow;
������ if(targetWindow != null)
������ {
�������������� varlb = newLabel{Content = "haha, i caught you :)"};
�������������� targetWindow.Content = lb;
������ }
}
����Ҳ�����f(shu��)InjectorDemo�M(j��n)�̕�(hu��)��InjectTargetApp�M(j��n)�̵������ڵă�(n��i)���ij�"haha, i caught you"�@�ӵ�һ��(g��)Label.
�����\(y��n)���:��
���� 
���������DƬ���������Ո(q��ng)�c(di��n)���@��鿴ԭ�D����D������
��������ăɂ�(g��)���ڷքe̎�ڲ�ͬ���M(j��n)����, �c(di��n)�� "Inject it" ���o, ���x�{(di��o)�����´��a:
ManagedInjector.Injector.Launch(targetProcess.MainWindowHandle, typeof(InjectorWindow).Assembly, typeof(InjectorWindow).FullName, "DoSomethingEvie");
����Ȼ��:
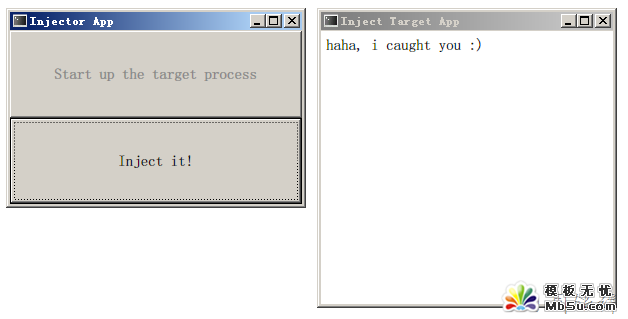
���������DƬ���������Ո(q��ng)�c(di��n)���@��鿴ԭ�D����D������
�������\Մʹ��ASP.NET Global.asax �ļ�Global.asax�ļ����Еr(sh��)�����ASP.NET��(y��ng)�ó����ļ����ṩ��һ�N��һ��(g��)����λ��푑�(y��ng)��(y��ng)�ó���(j��)��ģ�K��(j��)�¼��ķ����������ʹ���@��(g��)�ļ���(sh��)�F(xi��n)��(y��ng)�ó���ȫ���Լ�����һЩ�΄�(w��)�������҂�?c��)��?x��)��һ������ڑ�(y��ng)�ó����_(k��i)�l(f��)������ʹ���@��(g��)�ļ��� ���� Global.asaxλ��
- asp.net��εõ�GRIDVIEW��ij��ij��ֵ�ķ���
- .net SMTP�l(f��)��Email��(sh��)��(�Ɏ�����)
- js��(sh��)�F(xi��n)�V��Ư��Ч����С����
- asp.net Repeater ��(sh��)��(j��)�����ľ��w��(sh��)�F(xi��n)
- Asp.Net �o(w��)ˢ���ļ��ς����@ʾ�M(j��n)�ȗl�Č�(sh��)�F(xi��n)������˼·
- Asp.net�@ȡ�͑���IP��Ҋ(ji��n)���a���ڵĂ���IP��(w��n)�}̽ӑ
- VS2010 ˮ����(b��o)����ʹ�÷���
- ASP.NET�в���SQL��(sh��)��(j��)��(k��)(�B���ַ��������ü��@ȡ)
- asp.net�(y��)��?zh��n)�ֵ�y(c��)ԇ��(sh��)�����a
- DataGridView - DataGridViewCheckBoxCell��ʹ�ý�B
- asp.net��javascript������(ֱ��������g������)
- ����+�惦(ch��)�^(gu��)�̌�(sh��)�F(xi��n)���(y��)ʾ�����a
.Net�̳�Rssӆ����̳̽�����
.Net�̳����]
- ASP.NET��η�ֹ�Ñ���ε��
- ASP.NET�ĸ�(j��)�{(di��o)ԇ����
- asp.net�С��Ŀ͑����Йz�y(c��)���Н���Σ�U(xi��n)��Request.Formֵ�����e(cu��)�`
- AJAX���ɞ��Ƅ�(d��ng)Web2.0�r(sh��)�����x�_(k��i)�l(f��)ƽ�_(t��i)
- ASP.NET�W(xu��)��(x��)ƪ(1)�����_(k��i)ƪ
- �������M(j��n)ASP.NET(1)
- asp.net �@ȡ�͑���IP�cmac
- ASP.NET���õ���ʮ���N��(sh��)�ô��a
- Global.asaxȡ�^��(du��)·���ķ���
- ASP.NET��Session�Gʧԭ���c��Q����С�Y(ji��)
- ���P(gu��n)朽ӣ�
��(f��)�Ʊ��(y��)朽�| �������ӌ�(sh��)�F(xi��n).net������M(j��n)��ע��
- �̳��f(shu��)����
.Net�̳�-���ӌ�(sh��)�F(xi��n).net������M(j��n)��ע��
 ��
��